When you visit a website on your computer or mobile device, you are potentially sharing that information with advertisers, hackers, co-workers and governments. Even though the content you are viewing is likely to be encrypted with HTTPS, your metadata (including the URL and IP address of websites you visit, your IP address, the time and date, information about your web browser and computer hardware) can be collected and stored by anyone eavesdropping on the wire between you and the web server, to be used against you in targeted advertising campaigns, phishing scams, profiling, and soon robot assassination.
Wouldn’t it be nice if there was a way to use the internet with complete privacy, without anyone else knowing what you are reading about?
The Tor Browser (also available on Android) protects your privacy in two ways: first by providing a safer web browser that does not leak information about your computer or your browsing habits, and second by hiding your metadata with onion routing in the Tor network.
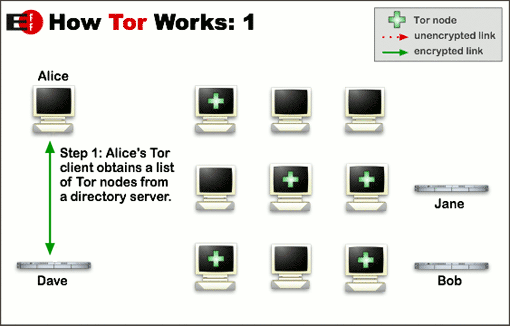
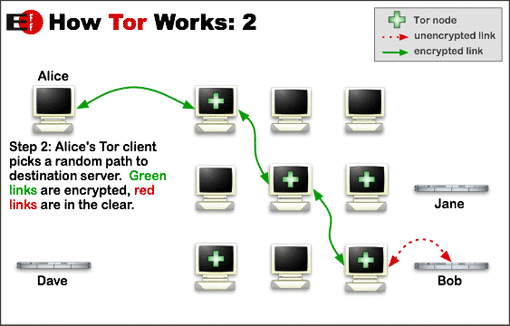
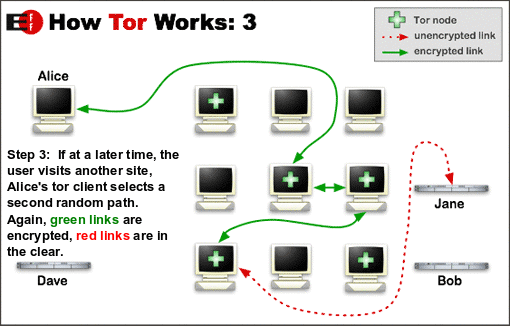
You type your URL (for example, https://google.com?q=global warming) into the Tor Browser. The browser looks up the list of Tor relay nodes from a directory server. These relays are computers run by volunteers to bounce your request around the world, hiding the true source and destination. The browser chooses several random relays to build a circuit.
Let’s assume your browser has chosen three relays named Optimus, Gandalf, and Hagrid to build a circuit. First the browser encrypts your URL in a message that only Hagrid can read. Then it encrypts Hagrid‘s message inside a message that only Gandalf can read. Then Gandalf‘s message is encrypted inside a message that only Optimus can read. Finally, your browser sends this multi-layered message (the onion) to Optimus, who decrypts the first layer and finds a message for Gandalf. Gandalf decrypts the second layer finding a message for Hagrid. Hagrid finds a request for https://google.com?q=global warming, which is retrieved and sent back to you through the circuit of relays.
- Optimus knows who you are, but it doesn’t know what is inside the message to Gandalf.
- Gandalf only knows that it is passing messages from Optimus to Hagrid.
- Hagrid knows which URL you are requesting, but it doesn’t know who you are. It only knows about Gandalf.
 Read more at Tor Project: Overview
Read more at Tor Project: OverviewAnother important feature of Tor is the ability to host a web server anonymously as a hidden service. This can protect you if you’re sharing knowledge and ideas that are unpopular or restricted by your government.
After you download the Tor Browser you can visit The Torist, a literature magazine only available through Tor, and the Facebook hidden service for users who wish to hide their real identity and browsing habits from Facebook’s sophisticated internet surveillance arsenal.
Find more at Wikipedia’s List of Tor hidden services.
